Login / Register
Software License Agreement
Micron Technology, Inc. Software License Agreement.
PLEASE READ THIS LICENSE AGREEMENT (“AGREEMENT”) FROM MICRON TECHNOLOGY, INC. (“MTI”) CAREFULLY: BY INSTALLING, COPYING OR OTHERWISE USING THIS SOFTWARE AND ANY RELATED PRINTED MATERIALS (“SOFTWARE”), YOU ARE ACCEPTING AND AGREEING TO THE TERMS OF THIS AGREEMENT. IF YOU DO NOT AGREE WITH THE TERMS OF THIS AGREEMENT, DO NOT DOWNLOAD THE SOFTWARE.
LICENSE: MTI hereby grants to you the following rights: You may use and copy the Software and redistribute it to third parties subject to the terms of this Agreement. You must maintain all copyright notices on all copies of the Software. MTI may make changes to the Software at any time without notice to you. In addition MTI is under no obligation whatsoever to update, maintain, or provide new versions or other support for the Software.
OWNERSHIP OF MATERIALS: You acknowledge and agree that the Software is proprietary property of MTI and is protected by United States copyright law and international treaty provisions. Except as expressly provided herein, MTI does not grant any express or implied right to you under any patents, copyrights, trademarks, or trade secret information. You further acknowledge and agree that all right, title, and interest in and to the Software, including associated proprietary rights, are and shall remain with MTI. This Agreement does not convey to you an interest in or to the Software, but only a limited right to use, copy and redistribute the Software in accordance with the terms of this Agreement. The Software is licensed to you and not sold.
DISCLAIMER OF WARRANTY: The Software is provided “AS IS” without warranty of any kind. MTI EXPRESSLY DISCLAIMS ALL WARRANTIES EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO, NONINFRINGEMENT OF THIRD PARTY RIGHTS, AND ANY IMPLIED WARRANTIES OF MERCHANTABILITY OR FITNESS FOR ANY PARTICULAR PURPOSE. MTI DOES NOT WARRANT THAT THE SOFTWARE WILL MEET YOUR REQUIREMENTS, OR THAT THE OPERATION OF THE SOFTWARE WILL BE UNINTERRUPTED OR ERROR-FREE. FURTHERMORE, MTI DOES NOT MAKE ANY REPRESENTATIONS REGARDING THE USE OR THE RESULTS OF THE USE OF THE SOFTWARE IN TERMS OF ITS CORRECTNESS, ACCURACY, RELIABILITY, OR OTHERWISE. THE ENTIRE RISK ARISING OUT OF USE OR PERFORMANCE OF THE SOFTWARE REMAINS WITH YOU. IN NO EVENT SHALL MTI, ITS AFFILIATED COMPANIES OR THEIR SUPPLIERS BE LIABLE FOR ANY DIRECT, INDIRECT, CONSEQUENTIAL, INCIDENTAL, OR SPECIAL DAMAGES (INCLUDING, WITHOUT LIMITATION, DAMAGES FOR LOSS OF PROFITS, BUSINESS INTERRUPTION, OR LOSS OF INFORMATION) ARISING OUT OF YOUR USE OF OR INABILITY TO USE THE SOFTWARE, EVEN IF MTI HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. Because some jurisdictions prohibit the exclusion or limitation of liability for consequential or incidental damages, the above limitation may not apply to you.
TERMINATION OF THIS LICENSE: MTI may terminate this license at any time if you are in breach of any of the terms of this Agreement. Upon termination, you will immediately destroy all copies the Software.
GENERAL: This Agreement constitutes the entire agreement between MTI and you regarding the subject matter hereof and supersedes all previous oral or written communications between the parties. This Agreement shall be governed by the laws of the State of Idaho without regard to its conflict of laws rules.
CONTACT: If you have any questions about the terms of this Agreement, please contact MTI’s legal department at (208) 368-4500.
By clicking on the Accept button, you agree to the terms of the License Agreement. You must agree to the terms in order to download the software.
Non-Disclosure Agreement
Micron Technology, Inc. NDA Agreement
To access these documents, you must first read and accept Micron's electronic non-disclosure agreement. If the Recipient has a written confidentiality agreement with Micron Technology, Inc. you will need to click "Accept" at the bottom of this page, but the terms of the written confidentiality agreement will apply.
ON-LINE NONDISCLOSURE AGREEMENT THIS IS A LEGAL AGREEMENT BETWEEN YOU OR THE COMPANY YOU REPRESENT (EACH A "RECIPENT") AND MICRON TECHNOLOGY, INC. ("MTI") STATING THE TERMS AND CONDITIONS THAT GOVERN THE CONFIDENTIALITY OF INFORMATION POSTED TO OR MADE AVAILABLE THROUGH THE MICRON WEBSITE. PLEASE CAREFULLY READ THIS NONDISCLOSURE AGREEMENT ("AGREEMENT") BEFORE CLICKING "ACCEPT" AT THE BOTTOM OF THE PAGE. BY CLICKING ON"ACCEPT", RECIPIENT IS AGREEING TO BE BOUND BY THE TERMS OF THIS AGREEMENT. IF RECIPIENT DOES NOT AGREE TO THE TERMS OF THIS AGREEMENT, PRESS "DECLINE" AND RECIPENT WILL BE UNABLE TO ACCESS CONFIDENTIAL INFORMATION.
1. Written Nondisclosure Agreement. If Recipient and MTI have entered into a written confidentiality agreement ("Confidentiality Agreement") that is in effect as of the date Recipient enters into this Agreement and such Confidentiality Agreement already applies to and governs the Confidential Information (defined below), then the terms of such Confidentiality Agreement shall apply to and govern Recipient’s obligations concerning such Confidential Information and not the terms of this Agreement.
2. Confidential Information. "Confidential Information" means any information or data posted to or made available through MTI’s secure website that is (i) marked or labeled as "Confidential" or "Proprietary" or with similar designation, or (ii) of a nature that a reasonable person would know such information is confidential. Confidential Information does not include that which:
(i) is proven by Recipient through competent evidence to rightfully have already been in Recipient's possession at the time of disclosure without an obligation of confidentiality;
(ii) is or becomes available to the public through no fault or breach on the part of Recipient;
(iii) is independently developed by Recipient without use of or reference to the Confidential Information;
or (iv) is rightfully obtained from a third party who has the right to transfer or disclose it to Recipient without restriction.
3. Purpose of Disclosure and Restriction on Use. Confidential Information is disclosed hereunder strictly for the purpose of Recipient’s internal evaluation and/or to assist Recipient in the implementation of an MTI device or product into a commercial product ("Purpose"). Recipient shall use the Confidential Information solely in accordance with the terms of this Agreement to accomplish the Purpose and shall make no further use, in whole or in part, of the Confidential Information.
4. Non-Disclosure. Recipient agrees to protect the Confidential Information, using at least the same degree of care it uses to protect its own confidential and proprietary information, but in no case with less than reasonable care. Recipient shall not disclose, publish or disseminate Confidential Information to anyone other than those of its employees, agents, contractors and consultants (collectively "Representatives") who have a need to know the information in order to accomplish the Purpose and who are bound by a written agreement that prohibits unauthorized disclosure or use of Confidential Information on terms no less restrictive and protective than those contained within this Agreement. Recipient will be responsible for any violation of the terms of this Agreement by its Representatives. Recipient may disclose Confidential Information to the extent required by law, provided Recipient shall promptly notify MTI in writing of such requirement to disclose and Recipient shall cooperate with MTI’s efforts to protect the Confidential Information. Recipient shall notify MTI promptly in writing in the event of any disclosure of the Confidential Information which is not authorized under this Agreement.
5. Feedback. Notwithstanding any other provision in this Agreement, if Recipient provides any ideas, suggestions or recommendations to MTI regarding Confidential Information ("Feedback"), MTI is free to use and incorporate such Feedback in MTI’s products, without payment of royalties or other consideration to Recipient, so long as MTI does not infringe Recipient’s patents, copyrights or trademark rights in the Feedback.
6. Copies. Recipient shall not make any copies of Confidential Information except as strictly necessary to carry out the above-stated Purpose. Any copies that are made must be identical to the original, may not be modified, and shall be considered the property of MTI.
7. No License. No Warranty. Except as expressly set forth herein, no license is granted hereunder to any patents, copyrights, mask works, or trademarks either expressly, by implication, estoppel or otherwise. Any such license must be express and in writing from MTI. All Confidential Information shall remain the property of MTI and nothing in this Agreement shall restrict MTI from using, disclosing or disseminating such Confidential Information in any way. CONFIDENTIAL INFORMATION IS DISCLOSED HEREUNDER "AS IS" WITHOUT ANY REPRESENTATIONS OR WARRANTIES OF ANY KIND WHATSOEVER INCLUDING, WITHOUT LIMITATION, ANY REPRESENTATIONS OR WARRANTIES AS TO THE ACCURACY, COMPLETENESS OR UTILITY OF SUCH CONFIDENTIAL INFORMATION.
8. Termination of Obligations of Confidentiality. This Agreement will become effective on the date Recipient clicks on "Accept." Notwithstanding any termination of this Agreement, the provisions of this Agreement shall continue for a period of five (5) years from the date of each disclosure of Confidential Information. MTI may terminate this Agreement at any time in its sole discretion upon written notice to Recipient (including such notice transmitted through this secure MTI website or via electronic mail to Recipient).
9. Return of Confidential Information. Within ten (10) business days of MTI’s written request, and at MTI’s option, Recipient shall return or certify to MTI the destruction of the Confidential Information including, without limitation, hard copy and electronic documents and all materials created by Recipient that contain the Confidential Information.
10. Governing Law and Attorneys' Fees. This Agreement shall be governed by the laws of the State of Idaho, U.S.A., excluding its conflict of laws principles. Recipient hereby consents to the personal jurisdiction of the courts of Idaho for any dispute arising out of this Agreement. In the event of any suit, action or proceeding arising out of or relating to this Agreement, the prevailing party will be entitled to reasonable attorneys' fees and reasonable costs incurred.
11. Export. Recipient agrees that Confidential Information, or any portion thereof, shall not be exported or re-exported, directly or indirectly, in any form, except in compliance with the U.S. Export Administration Act and all other applicable export control laws or regulations.
12. Injunctive Relief. Recipient acknowledges and agrees that disclosure of Confidential Information in violation of the terms of this Agreement will cause irreparable harm to MTI for which monetary damages would not be an adequate remedy. Therefore, Recipient agrees that, in addition to any other remedies available to MTI, in the event of any breach or threatened breach of this Agreement, MTI shall be entitled to injunctive relief and Recipient waives any requirement for the posting of a bond in connection therewith.
13. No Implied Waiver. MTI’s failure or delay in exercising any of its rights hereunder will not constitute a waiver of such rights unless expressly waived in writing.
14. General. This Agreement:
(i) may be amended or modified only by an express writing signed by Recipient and an authorized representative of MTI;
(ii) will not be construed as creating any joint venture, partnership or other form of business association between the parties hereto;
(iii) is not assignable or delegable in whole or in part by Recipient without the express written consent of MTI;
(iv) shall inure to the benefit of and be binding upon the parties, their successors, the assigns of MTI and the permitted assigns of Recipient;
and (v) is in the English language only, which language shall be controlling in all respects, and all versions of this Agreement in any other language shall not be binding on the parties hereto.
15. Authorized Signatory. The individual clicking on "Accept" is entering into this Agreement and accessing Confidential Information either (1) as an individual, and hereby agrees that he or she shall be personally liable to MTI if Confidential Information is disclosed or used in a manner not authorized by this Agreement, or (2) on behalf of an employer or other entity, and hereby represents and warrants that he or she has full legal authority to bind such employer or entity to this Agreement and that such employer or entity shall be legally bound by all of the terms and conditions of this Agreement as Recipient hereunder. IF CONFIDENTIAL INFORMATION IS FOR AN EMPLOYER OR ENTITY, BUT YOU DO NOT HAVE THE LEGAL AUTHORITY TO SO BIND SUCH EMPLOYER OR ENTITY, THEN DO NOT ACCESS, VIEW, READ, OR DOWNLOAD IN ANY WAY CONFIDENTIAL INFORMATION, AND DO NOT CLICK ON "ACCEPT."
In order to review documents, you must accept the NDA. If you do not accept these terms, select Decline to exit this menu.
Secure document access request Process
Thanks for being logged in as a registered micron.com user.
The document you are requesting requires some additional information. This information must be provided even if you have provided it in the past. Providing this information again could be necessary because Micron must validate your access.
Please complete the forms you are provided. This may consist of one or two forms:
- Secure document access request form
This form enables us to verify your company has a non-disclosure agreement (NDA) with Micron covering secure content, and confirms you are approved to view the document. If you have completed this form in the past for this document, you will not be prompted to fill out this form.
- End user certification (EUC) form
This form ensures your company complies with export controls. If your company has a valid EUC, you will not be prompted to fill out this form.
Secure document access request process FAQ
After you submit the requested form(s), access can take up to 10 days. You will receive an email confirming receipt of your submitted form(s).
If you have questions about your submission or this process, please contact Micron using the Contact us form.
Login
Welcome to Micron.com, please Log in or Register an account to continue.
Export Compliance Certification (ECC)
Micron Technology Inc. ECC Agreement
In furtherance of Micron’s compliance with the requirements of the United States Export Administration Regulations (“EAR”) as administered by the U.S. Department of Commerce, and the regulations of the Office of Foreign Assets Controls (“OFAC”) (31 C.F.R. 500-599) as administered by the U.S. Department of Treasury YOUR COMPANY acknowledges that the access to commodities, software and/or technology (items) that are being provided to them by Micron are subject to these regulations. By executing this Certification, YOUR COMPANY acknowledges and certifies that it will comply with the requirements described herein and accept responsibility for any subsequent transfers of the products, software, or technology (herein referred to as “Items”).
Accordingly, YOUR COMPANY hereby acknowledges and agrees to the following terms and conditions:
YOUR COMPANY will comply with applicable U.S. export control laws, regulations, and requirements.
YOUR COMPANY will not knowingly transfer, export, re-export, or divert any Micron items, directly or indirectly to any person, country, or to any foreign national or resident thereof, without first obtaining, if so required, all export licenses, authorizations and/or approvals from the U.S. Department of Commerce or other appropriate U.S. governmental agencies.
YOUR COMPANY will not export, re-exports and or transfer directly or indirectly any Micron products, software, or technology to sanctioned entities and individuals who are prohibited from receiving U.S. Items and certain other Items or services.
YOUR COMPANY will not export, re-exports and or transfer directly or indirectly any Micron products, software, or technology to these countries: the Crimea Region (including the Donetsk People’s Republic (DNR) and Luhansk People’s Republic (LNR regions), Russia, Belarus, Cuba, Iran, North Korea, and Syria. All sales, exports, re-exports and transfers directly or indirectly to these countries involving Micron Items are prohibited.
YOUR COMPANY will not knowingly engage in activity related to the development, production, use, or maintenance of Weapons of Mass Destruction, as defined by the U.S. Department of Commerce, including without limitation, uses related to nuclear, missile, chemical or biological warfare. Nor will we knowingly transfer, export, or re-export directly or indirectly to any party engaged in such activity.
YOUR COMPANY will not engage in, or knowingly sell to any party engaged in activity related to the development, production, use, or maintenance of any safeguarded or unsafeguarded nuclear fuel facility or components for such facilities as follows: a. Facilities for the chemical processing of irradiated special nuclear or source material; b. Facilities for the production of heavy water; c. Facilities for the separation of isotopes of source and special nuclear material; or d. Facilities for the fabrication of nuclear reactor fuel containing plutonium.
YOUR COMPANY certifies it is not a military entity or end-user and will not transfer, export, re-export, or divert any Micron items, for the production or support of military end uses or for military end users. For purposes of this Agreement, a “military end use” means (i) incorporation of an item into a military item or (ii) any item that supports or contributes to the operation, installation, maintenance, repair, overhaul, refurbishing, development, or production, of military items. A “military end user” is (i) a national armed service (army, navy, marine, air force, coast guard, national guard, or national police); (ii) a government intelligence or reconnaissance organization; or (iii) any person or entity whose actions or functions are intended to support “military end uses.”
YOUR COMPANY certifies will not transfer, export, re-export, or divert any Micron items, for the development, production, use, or maintenance of integrated circuits (ICs) at a semiconductor fabrication facility located in China or Hong Kong. These restrictions also prohibit the use of Micron products, technology and/or services for supercomputing.
By signing this Certification and Agreement, you certify on behalf of YOUR COMPANY not to export, re-export, or transfer Micron Items in violation of any applicable export control laws or regulations, including the laws of the United States. YOUR COMPANY further certifies that it will promptly correct or supplement this Certification if Company is no longer able to make these representations or learns that information changed.
By clicking Accept, you hereby acknowledge and certify your company’s acceptance and agreement hereto and represents that you have full legal authority to bind Company hereto.
Our commitment starts here
At Micron, our commitment to excellence is anchored in our steadfast dedication to comprehensive security for our solutions, driven by our relentless focus on quality.
In today’s data-centric world, security is of paramount importance. IT managers, chief information officers (CIOs), chief information security officers (CISOs) and everyday consumers face ever-increasing threats from cybercriminals attempting to access and acquire private, sensitive and valuable data. These threats call for layered data protection that secures both data in flight, data being transferred into and from storage or memory devices, and stored data, that resides within a storage or memory device.
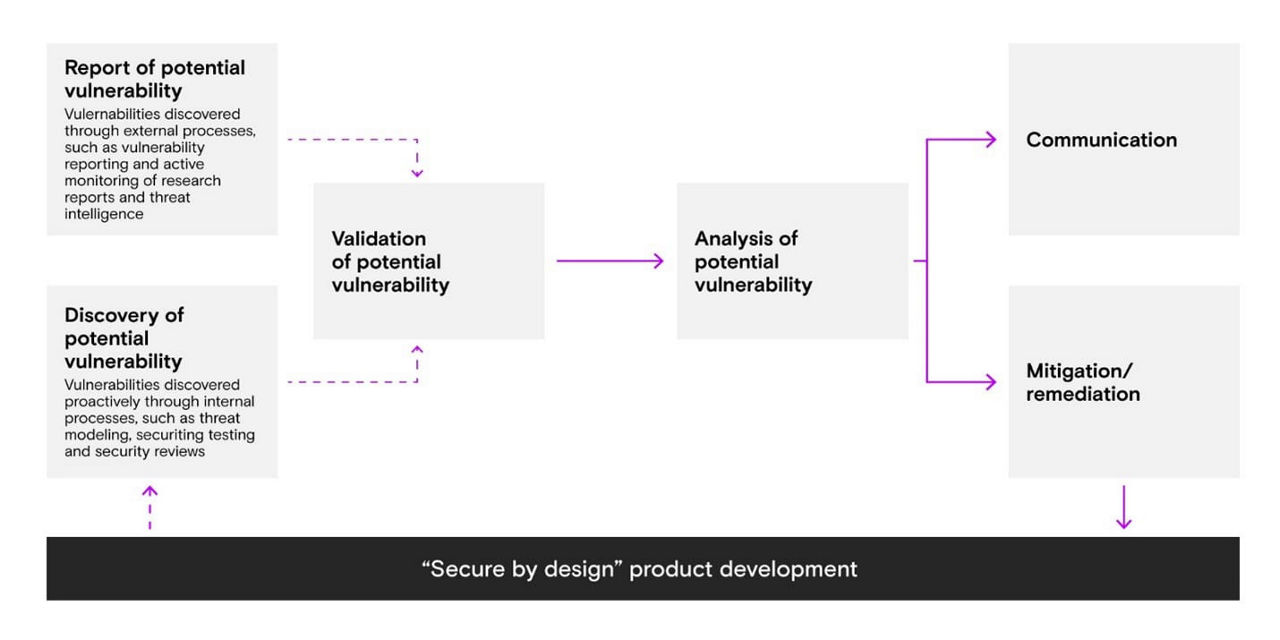
Micron integrates robust security features into our product designs, such as implementing secure boot processes, establishing a hardware root of trust, encrypting data where applicable, and implementing standardized security features.1 Our “security by design” approach integrates security as a core product and business requirement, increasing our resilience to evolving security threats.
Note that no hardware, software, or system can provide absolute security against all threats, so education on best practices to avoid things like spearfishing attacks is critical for individuals and organizations.
We take security seriously. If you have an issue or concern, report it at our
Defending your data
Micron products are designed to fortify your most critical data.
Products
- Micron DRAM and HBM
- Micron SSD
- Micron NAND Components
- Micron Managed NAND
- Micron NOR
Micron DRAM and HBM
Micron DRAM products meet or exceed JEDEC standards that are collaboratively developed by the industry. This consortium includes a dedicated task group on security and data integrity. In addition to designed-in security features, the inherent operation of DRAM requires constant power. Physically removing the device from the system will disturb programmed content.
Micron was first in the memory industry to certify a DRAM product to ASIL D, the highest level of ISO 26262 functional safety requirements. Our proprietary product safety features use existing JEDEC supported pins and mode registers and are developed to improve diagnostic coverage of transient and permanent faults. One such feature is our Testmode Entry Flag. This feature will alert the host to the use of modes that could represent attacks if the host did not specifically request these actions.
DRAM security related assets
- See the Micron DRAM in Safety Critical Automotive Systems for more information.
- Learn more about Micron’s drive for automotive.
- Read JEDEC’s press release on the DDR5 standard.
- See the Micron DDR5 SDRAM site for additional information.
- Learn about Micron’s quality certifications (micron.com).
Micron SSD
Micron customers trust our products to store and help protect their most critical and sensitive data. That is why we build security into the design of our SSDs with robust encryption and authentication features, as well as data sanitization methods consistent with industry standards. We also test the security of our data center SSDs and other select products at key development milestones to ensure they are hardened against known attacks.
Our Micron-branded SSD portfolio includes robust security features and is designed to meet our customers’ needs, which often go beyond those specified by industry groups for trusted computing platforms.1 We use numerous methods to enhance the security of data across various SSDs in our portfolio.
Micron integrates features focused on platform-level security:
Security Protocol and Data Model2 (SPDM): Defines messages, data objects and sequences for performing message exchanges between devices over a variety of transport and physical media.
Micron secure execution environment (SEE): A dedicated security processor consisting of dedicated ROM, firmware and a security microprocessor. The secure microprocessor is electrically isolated from other microprocessors within the SSD controller and SEE execution cannot be preempted by nonsecure code. This isolation significantly reduces the opportunity for the security functionality of the storage device to be accidentally or maliciously circumvented.
Micron helps secure data upon SSD retirement or repurpose with features like these:
Cryptographic erase: Erasing a self-encrypting drive (SED) by permanently destroying the encryption key.
- Sanitize: Removing data from the storage device to a point that exceeds the ability to reconstruct the data by known forensic means.
- Secure erase: Executing a block erase on each element in the NAND flash array in the SSD.
Micron supports data security when debugging SSDs in the data center by utilizing mechanisms designed to provide helpful diagnostic information without exposing user data and blocking access through dedicated debug ports on shipping drives. We also validate our cryptographic functions through red team testing, and on some products seek FIPS certification.
Furthermore, to help combat malicious digital tampering:
Attestation: Uses a secure mechanism to validate trust in server components such as SSDs.
- Secure boot: Uses a trust relationship between different entities where each entity honors the other’s authenticity, and each step is subject to attestation prior to execution (such as during power-on). Micron SSD secure boot uses a chain of trust mechanism in which the SSD firmware bootloader trusts the immutable SSD ROM, and the main firmware, in turn, trusts the bootloader.
- Signed firmware: Authenticates SSD firmware prior to updating it, which helps protect our SSDs against malicious firmware.
- In addition to the above security, Micron SSDs are designed to provide additional data protection by implementing standards-based encryption and other security mechanisms. By leveraging industry-specified mechanisms, Micron facilitates rapid adoption of data security, as well as broad interoperability.
- Trusted Computing Group (TCG)3 Pyrite: A standard that provides basic security but does not support user data encryption.
- TCG Opal: A standard designed to provide more advanced security than Pyrite. The Opal standard can be used to encrypt user data in SEDs.
- TCG Enterprise: A standard designed to help protect against data loss due to theft of physical storage devices.
- eDrive: A combination of IEEE-1667 and TCG Opal that works with Windows BitLocker to help encrypt the contents of the SSD.4
- Hardware security engines: Micron deploys encryption engines such as AES-256, RSA 4096, and SHA-512 in select SSDs. These engines meet or exceed key security standards specified in the Commercial National Security Algorithm (CNSA) Suite document.
SSD security-related assets
- For a list of the security features supported by Micron SSDs, read the Micron SSD security features flyer, confirm the capabilities of your specific part number, and consult with Micron technical support.
- For an overview of SSD security terms, read the Micron Technical Brief: SSD Security Features.
Note that not all security features are implemented on all product families or all product SKUs within a family.
1 For the current portfolio of Micron SSDs. Standards referenced are those mentioned in the SSD section of this page, such as TCG, SPDM and eDrive.
2 The DMTF website offers additional information on SPDM.
3 Trusted Computing Group security standards (“TCG standard”) include TCG storage security subsystem classes Opal, Pyrite, and Enterprise.
4 This page on Microsoft's website offers additional details on BitLocker
Micron NAND components
Micron NAND devices are used in a wide variety of systems where cost-effective nonvolatile memory is needed. Micron NAND devices are designed to meet and exceed the ONFI and JEDEC standards for NAND that are collaboratively developed by those open-membership industry-leading consortiums.
Micron NAND devices enable commonly used best practices for data integrity, error recovery and access control, allowing host data to reside in a robust device that will meet the performance and reliability needs of the wide variety of systems that use NAND. These are some of the more notable security features available in select NAND products:
- Read unique ID: All Micron NAND supports an identifier programmed into the device that allows host systems to uniquely identify a NAND device.
- One-time programmable storage: All Micron NAND supports a one-time-programmable (OTP) area outside the main flash array where customers can program their unique data. The OTP functionality allows a host system to lock data programmed into the OTP area from being modified.
- Block lock and protect: Select Micron low-density NAND devices support block lock and protect functionality, allowing a host system to lock data programmed in ranges of block addresses, protecting it from being modified. Contact your local Micron field support representative to understand what features are available on these devices.
NAND related assets
Micron Managed NAND
Micron offers a full range of secure managed NAND products to meet the storage needs of a broad array of solutions. Our fully managed devices — including uSD, eMMC, and UFS — handle media management and error correction code (ECC) internally to help make technology transitions more seamless.
Managed NAND products released after April 2019 support an authenticated firmware update mechanism as described in NIST 800-193 Platform Firmware Resiliency Guidelines.
Managed NAND and component-specific security features
Managed NAND products released after April 2019 support the following features:
- Authenticated firmware update: Designed with an RSA signature for firmware binaries and public keys in ROM, checked both during manufacturing flow and field firmware update (FFU). Hash Message Authentication Code (HMAC) signature check, based on secret and device-unique keys, performed by ROM at each boot.
- Disabling debug ports in production parts: Executed with required host authentication (based on RSA) for unlocking debug ports for failure analysis.
- Encryption of security-critical parameters at rest: Designed to help protect against physical attacks (e.g., RPMB keys).
Note that not all security features are implemented on all managed NAND product families or all product SKUs within a family.
Micron NOR
NOR devices are typically used in system boot environments where high reliability, low latency and granular data access are desired. While few security industry standards exist for core NOR functionality, Micron NOR devices enable commonly used best practices for data integrity and access control, allowing user content to reside in a robust device that will perform the system-critical boot process in a reliable manner.
- Baseline block locking: Micron NOR devices offer several forms of block locking that are customer-configurable based on their unique system requirements. Blocks may be protected from malicious and spurious manipulation in several ways, including command-based volatile and nonvolatile locking and password locking. Once a block is locked, it becomes read-only, ensuring data integrity and reliability.
- Advanced block locking: Micron Xccela™ MT35X and select Quad SPI MT25Q part numbers offer additional block locking capabilities, such as range-based block locking with status and management configuration registers.
- Unique ID: Micron NOR devices come with a 64-bit, 14-to-16-byte unique identifier code.
- One-time programmable storage: Micron Quad SPI MT25Q and Xccela MT35X devices each have a 64-byte, one-time-programmable area outside the main flash array where customers can set their own unique identifiers. The Micron MT28EW devices expand this area to 1KB. This built-in feature facilitates inventory control, traceability or similar functions by the customer.
- Replay-protected monotonic counter (RPMC): Micron Quad SPI MT25Q product lines add four integrated monotonic counters on select part numbers, which may only be incremented by a host with knowledge of a secret 256-bit cryptographic key. The contents of each counter are also cryptographically verifiable by the host. This enables one-time use numbers from each counter that preserve uniqueness and help to make systems more resistant to rollback and replay attacks.
NOR security-related asset
- Learn more about NOR flash here Versatility: Easy, Scalable, Efficient NOR Flash.
Micron security resources
If you have an issue or concern, report it at our product security and vulnerability reporting site. Contact your Micron account representative for additional details on these practices.
1 Micron assumes no liability for lost, stolen, or corrupted data.